Intro
Lately, I often use automatic recon tools to exploit errors, partly because of simplicity, partly because I help to ignore basic errors that are not worth it, especially with a large number of sub-domains, or scope. Wide range of programs.
During the time searching for automatic tools that can simplify the recon website, the person sitting next to me suggested a pretty good tool. Nuclei
So why am I writing this article, I think Nuclei is quite good, has many modules, can customize rules freely, …
Some information about Nuclei:
- Github: https://github.com/projectdiscovery/nuclei
- Home page: https://nuclei.projectdiscovery.io/
- Blog: https://blog.projectdiscovery.io/
Install Nuclei
The installation is very simple and not complicated, there are 3 ways to install Nuclei on your VPS (here I use VPS to save power and run recon on it to avoid affecting real hardware hardware) :
Option 1: Install using binary
1 2 3 4 5 6 | Tải binary mới nhất tại https://github.com/projectdiscovery/nuclei/releases ▶ tar -xzvf nuclei-linux-amd64.tar.gz #Giải nén ▶ mv nuclei /usr/local/bin/ #Di chuyển file binary vào path để gọi ở bất cứ đâu ▶ nuclei -version #Kiểm tra đã cài đặt xong chưa |
Method 2: Installation is taken directly from the source
Nuclei requires to install go1.14 or higher, after you install go1.14 + then run this command to be able to use the nuclei.
1 2 | ▶ GO111MODULE=on go get -u -v github.com/projectdiscovery/nuclei/v2/cmd/nuclei |
Method 3: Installation is still from source, but in another way
1 2 | ▶ git clone https://github.com/projectdiscovery/nuclei.git; cd nuclei/v2/cmd/nuclei/; go build; mv nuclei /usr/local/bin/; nuclei -version |
Installation is complete, but we have not used the nuclei yet, the nuclei can run when using rules, however the nuclei does support templates which are available to download by
1 2 | nuclei -update-templates |
Or can be downloaded from Github
1 2 | git clone https://github.com/projectdiscovery/nuclei-templates.git |
Launch Nuclei
There are quite a few ways to use Nuclei, you can learn through --help , here I am the basic user guide ^^;
Running Nuclei with 1 template
For example, we have a list of domains, we need to check whether in this domain list there is a .git directory error configuration, run the command
1 2 | nuclei -l urls.txt -t files/git-core.yaml -o results.txt |
with
urls.txtsummarizes the list of domains to testfiles/git-core.yamlis the test template fileresults.txtis the output file to check later.
Run Nuclei with all templates
This is how I often use, run all of it, I would rather kill the mistake than miss it, run the whole thing as if about 350 templates are right, or have the template updated, you can read the log on the homepage.
1 2 | nuclei -l urls.txt -t nuclei-template/ -o results.txt |
Run Nuclei with template exclusion feature
Run the template based on severity
1 2 | nuclei -l urls.txt -t nuclei-template/ -severity critical, medium |
With this command, the nuclei will only run templates that are marked critical as critical and medium.
Run the entire template but exclude a few directories
1 2 | nuclei -l urls.txt -t nuclei-templates -exclude panels/ -exclude files/wp-xmlrpc.yaml |
There are many more features of nuclei waiting for you to discover
Writing template for Nuclei
Here we use a template available of Nuclei looking for directory traversal errors
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 | <span class="token key atrule">id</span> <span class="token punctuation">:</span> directory <span class="token punctuation">-</span> traversal <span class="token key atrule">info</span> <span class="token punctuation">:</span> <span class="token key atrule">name</span> <span class="token punctuation">:</span> Generic Directory Traversal <span class="token key atrule">author</span> <span class="token punctuation">:</span> pentest_swissky <span class="token key atrule">severity</span> <span class="token punctuation">:</span> high <span class="token key atrule">description</span> <span class="token punctuation">:</span> Detect basic directory traversal leading to a leak of sensitive files. <span class="token key atrule">requests</span> <span class="token punctuation">:</span> <span class="token punctuation">-</span> <span class="token key atrule">method</span> <span class="token punctuation">:</span> GET <span class="token key atrule">path</span> <span class="token punctuation">:</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/..%5c..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/..%5c..%5c..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/..%5c..%5c..%5c..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/..%5c..%5c..%5c..%5c..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/static/..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/static/..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/static/..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/static/..%5c..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/static/..%5c..%5c..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/static/..%5c..%5c..%5c..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/static/..%5c..%5c..%5c..%5c..%5c..%5c..%5cetc/passwd"</span> <span class="token punctuation">-</span> <span class="token string">"{{BaseURL}}/./../../../../../../../../../../etc/passwd"</span> <span class="token key atrule">matchers-condition</span> <span class="token punctuation">:</span> and <span class="token key atrule">matchers</span> <span class="token punctuation">:</span> <span class="token punctuation">-</span> <span class="token key atrule">type</span> <span class="token punctuation">:</span> status <span class="token key atrule">status</span> <span class="token punctuation">:</span> <span class="token punctuation">-</span> <span class="token number">200</span> <span class="token punctuation">-</span> <span class="token key atrule">type</span> <span class="token punctuation">:</span> regex <span class="token key atrule">regex</span> <span class="token punctuation">:</span> <span class="token punctuation">-</span> <span class="token string">"root:[x*]:0:0:"</span> <span class="token key atrule">part</span> <span class="token punctuation">:</span> body |
Here we can see, this template is divided into 3 parts
- Part 1: specify the id name of this template
directory-traversal - Part 2: Here write all information related to this vulnerability, what is the name, who is the writer, how dangerous is it, how to describe the vulnerability.
- Part 3: This part is the most important part, it will show the Nuclei how to run the request, how the results will be determined when it is an error, …
The complete instruction to write template of nuclei is available at https://nuclei.projectdiscovery.io/templating-guide/ , hope you can write good templates to contribute to the nuclei.
Result
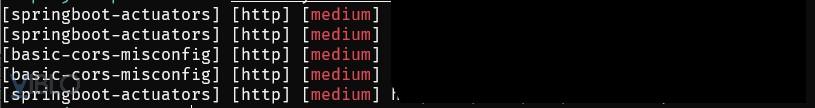
Some loopholes I have found when using Nuclei

Command I often use is
1 2 | A=<domain>;subfinder -d $A | httprobe | tee ~/sub-domain/$A | nuclei -t nuclei-templates/ -o ~/project-pentest/$A-output.txt |
