I. What is Blockchain Technology?

Blockchain, originally called block chain – is a ledger that records the balance and history information of all accounts participating in its transaction chain. Each block containing information in the blockchain system is often called a “block”. The blocks contain information about the initialization time and are linked to the previous block, accompanied by a time code and transaction data. Once the data is accepted by the network, there is no way to change it. Therefore, it can be said that Blockchain was born to prevent fraud and change of data in transactions.
More specifically, a blockchain is a linear chain of blocks connected and secured by cryptographic proofs. A blockchain is often built as a distributed system that functions as a decentralized ledger. This means that there are multiple (distributed) ledgers and no single organization has the (decentralized) control. Put simply, every user participating in the blockchain network will keep an electronic copy of blockchain data. Blockchain data is regularly updated with all the latest transactions and synchronized with the user’s copy.
In other words, a distributed system is maintained by the collective work of many users around the world. These users are also called network nodes, and all these nodes are involved in the process of verifying and validating transactions according to the rules of the system. Therefore, power is decentralized. Blockchain technology can also be applied in other areas that do not necessarily require financial activities. In the context of cryptocurrencies, blockchain has the role of permanently keeping a record of all confirmed transactions.
II. Blockchain History?
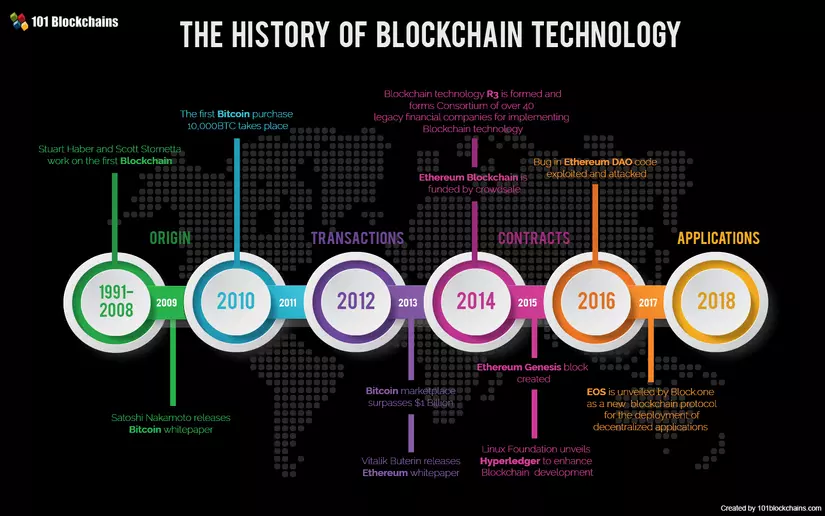
The idea behind blockchain technology was described as early as 1991 when researchers Stuart Haber and W. Scott Stornetta introduced a practical, computational solution to timestamp digital documents so that they would not be blocked. backdating or intervening. The system used a string of cryptographically secured blocks to store timestamped documents, and in 1992, Merkle trees were integrated into the design, making it more efficient. by allowing a block to gather some text. However, this technology was not used and the patent expired in 2004, four years before Bitcoin was born.
In 2004, computer scientist and cryptographer Hal Finney (Harold Thomas Finney II) launched a system called RPoW, Proof Of Work Reuse. The system works by receiving an immutable or irreplaceable Hashcash based on the proof of work token, and in return creates an RSA signed token that can then be exchanged directly from this person. to other people. RPoW solved the problem because of double consumption by keeping ownership of registered tokens on a trusted server; This server is designed to allow users around the world to verify accuracy and integrity in real time. RPoW can be seen as an initial experiment and is an important first step in the history of cryptocurrencies.
At the end of 2008, a white paper introducing a peer-to-peer, decentralized electronic cash system – Bitcoin, was posted on the crypto mailing list by a person or organization that took the nickname. is Satoshi Nakamoto. Based on the proof of work Hashcash algorithm, but instead of using a hardware-based calculation function like RPoW, the double spending protection feature in Bitcoin is provided by a peer-to-peer network protocol for tracking and authentication. transactions. In short, miners “mine” Bitcoin for rewards using a proof-of-work mechanism and then verify with decentralized nodes in the network. On January 3, 2009, Bitcoin was born when Satoshi Nakamoto dug up the first bitcoin block, giving him a 50 bitcoin reward. The first recipient of Bitcoin was Hal Finney, who received 10 bitcoins from Satoshi Nakamoto in the world’s first bitcoin transaction on January 12, 2009.
III. The principle of operation of Blockchain
1. Coding principle
In fact, the ledger is always maintained by computers in the peer network that are connected to each other. Therefore, it will have some differences:
In the banking system, we only know our own transactions and account balances, so on the bitcoin blockchain you can see everyone’s transactions. third-party acts as an intermediary to process transactions.The blockchain system is designed in a way that does not require the reliability and assurance provided by the special mathematical encryption functions. To be able to conduct transactions on the blockchain, you need a software that will allow you to store and exchange your Bitcoin coins called digital wallets. This e-wallet will be protected by a special encryption method that uses a unique security key pair: the private key and the public key.
If a message is encrypted with a specific public key, only the owner of the private key, a pair with the public key, can decrypt and read the message.
When encrypting a transaction request with a private key, you are creating an electronic signature used by computers in the blockchain network to check the sender and the authenticity of the transaction. This signature is a text string and a combination of your transaction request and private key.
If a single character of this transaction request message is changed, the digital signature will change accordingly. Therefore, it is difficult for hackers to change your transaction requirements or change the amount of Bitcoin you are sending. 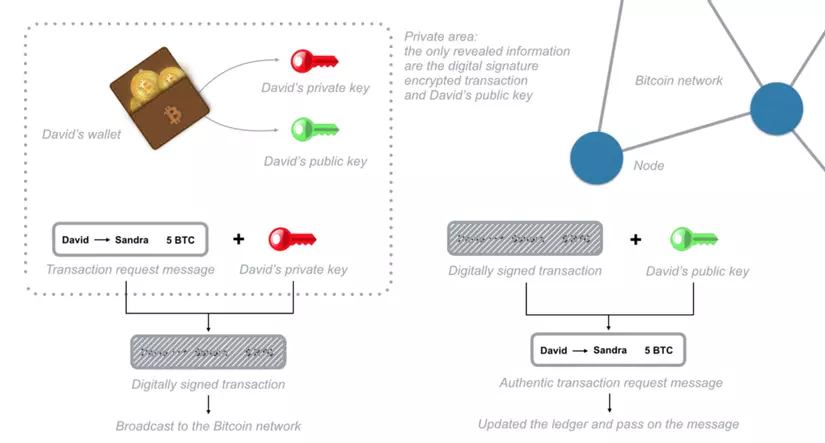
In order to send Bitcoin (BTC), you need to prove that you own the private key of a specific electronic wallet because you need to use it to encrypt transaction request messages. Once your message has been sent and encrypted, you don’t need to reveal your private key anymore.
2. Rules of the ledger
Each node in the blockchain is keeping a copy of the ledger. Therefore, each node knows what your account balance is. The blockchain system only records each requested transaction, not your account balance.
To know the balance on your e-wallet, you need to authenticate and confirm all transactions that took place on the network related to your e-wallet. 
This “balance” verification is done using calculations based on links to previous transactions. Looking at the picture above, to send 10btc to John, Mary needs to create a transaction request that includes links to previous transactions with balances equal to or exceeding 10 btc.
These links are considered as input values, nodes in the network will verify whether the total amount of these transactions is equal to or exceeds 10 btc. All this is done automatically in Mary’s digital wallet and checked by nodes on the Bitcoin network, Mary only sends a 10 bitcoin transaction to John’s wallet using John’s public key. 
So, how can the system trust these input transactions and validate them?
The fact is that the nodes will check all transactions related to the cryptocurrency wallet you used previously to send Bitcoin (BTC) through a reference of the transaction history. Having a record will store the unused BTC and stored by network nodes to help simplify and speed up the verification process. Therefore, cryptocurrency wallets avoid double spending.
=> “So owning Bitcoin means having transactions stored in the ledger linked to your wallet address that haven’t been used as an input transaction yet.”
The source code on the Bitcoin network is open source, which means that anyone with a computer connected to the internet can join the network and conduct transactions.
However, if any error in the source code is used to issue a transaction request message, the associated Bitcoin will be permanently lost.
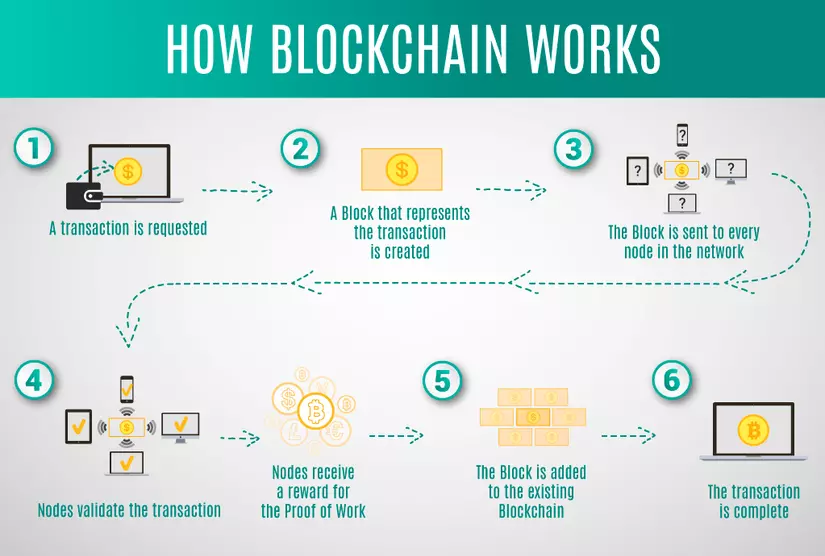
3. Principles of creating blocks
Transactions after being posted on the blockchain network will be grouped into blocks and transactions in the same block (block) are considered to have occurred at the same time. Unscheduled transactions in 1 block are considered as unconfirmed.
Each node can group transactions together into a block and send it to the network as an implication for subsequent blocks to be attached later.
Any button can create a new block. So the question is: which block will the system agree with? Which block will be the next one?
To be added to the blockchain, each block must contain a piece of code that acts as an answer to a complex mathematical problem generated by the irreversible hash function.
The only way to solve such a mathematical problem is to guess random numbers, numbers that, when combined with the previous block content, produce a system-defined result. This can sometimes take about a year for a typical computer with a basic configuration that can correctly guess the answer numbers for this math problem.
The network specifies that each block is created every 10 minutes, because there are always a large number of computers in the network focusing on guessing this sequence. Any node that solves such a mathematical problem will be allowed to attach the next block to the chain and send it to the entire network.
So what happens if two nodes solve the same problem at the same time and transmit their resulting blocks simultaneously to the network? In this case, both blocks are sent to the network and each node will build the next block on the block it receives first.
However, the blockchain system always requires each node to build on the longest block chain it receives. So, if there is any confusion about which block is the last, then as soon as the next block is solved, each node will apply to the longest chain. 
Because the probability of building blocks simultaneously is very low, it is almost impossible for many blocks to be solved at the same time and many times create different blocks. Therefore, the entire block-chain will quickly stabilize and merge when all nodes are in consensus.
4. Blockchain security algorithm
If there is any disagreement about the last representative block of the chain, this will lead to the possibility of fraud. If a transaction occurs in a block that belongs to a shorter tail when the next block is processed, that transaction will revert to an unconfirmed transaction because all other transactions are grouped into the other block.
Transactions in the bitcoin blockchain network are protected by a mathematical race: with any attacker who wants to compete with the entire network.
As a result, transactions become safer over time. And blocks that have been added to the chain in the past are always safer than newly added blocks. Because a block is added to the chain on average every 10 minutes, about 1 hour after a transaction is grouped into its first block creates a high probability that the transaction has been processed and cannot reverse.
IV. Main features of Blockchain technology
Blockchain technology is like a ledger recording all transactions that occur in the system. The main features of blockchain are as follows:
- Cannot be fake, can’t destroy blockchain chains: Blockchian chains are nearly indestructible, and in theory only quantum computers can interfere and decode blockchain chains and it only be completely destroyed when there is no internet on the globe
- Immutable: The data in the blockchan is almost immutable (only editable by the person who created it, but with the consent of the nodes on the network) and that data will be kept forever. forever
- Data Security: The information and data in blockchain chains are absolutely distributed and secure only the holder of the private key can access that data.
- Transparency: Anyone can follow the path of data in the blockchain from address to address and can statistics the entire history on that address.
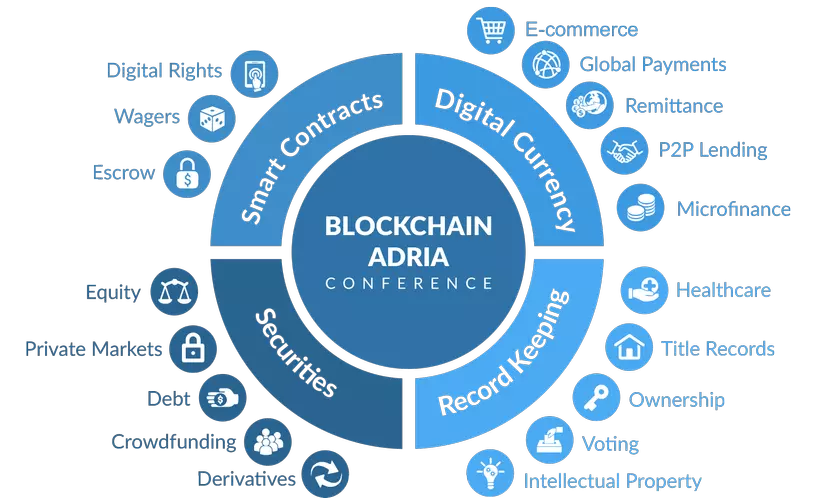
- Smart contracts: are digital embedded by an if-this-then-that (IFTTT) code in the system, allowing them to execute without third parties. The blockchain does not need a third party to join the system, and it ensures that all participants know the contract details and the terms will be automatically executed once the conditions are met.
V. Types in Blockchain system
In the Blockchain system, there are 3 main types:
- Public: This is a blockchain system that anyone can read and write data on. The process of authenticating transactions on Blockchain requires thousands or even thousands of nodes to participate. Therefore, it is impossible to attack this Blockchain system because of the high cost. Examples of public blockchain: Bitcoin, Ethereum …
- Private: This is a blockchain system that allows users to only read data, not write because this belongs to an absolutely trusted third party. This third party may or may not allow users to read data in some cases. The third party is free to decide all changes on Blockchain. Because this is a Private Blockchain, the transaction confirmation time is quite fast because only a small number of devices are required to authenticate transactions. For example, Ripple is a type of Private Blockchain, this system allows 20% of nodes to be fraudulent and only needs the remaining 80% to operate stably.
- Permissioned: Also known as the Consortium, is a form of Private Blockchain but adds certain features, combining “belief” when joining Public and “absolute belief” when joining Private. For example: Banks or financial institutions will use their own Blockchain.
BECAUSE. Versions in the Blockchain system
Currently, blockchain technology has 3 main versions:
- Blockchain 1.0 – Currency and Payment: As a primitive and first version of blockchain, the main application of this version is the work related to cryptocurrencies: including currency conversion, remittances and creation set up a digital payment system. This is also a field familiar to many people, sometimes quite a few people mistakenly think Bitcoin and Blockchain are one.
- Blockchain 2.0 – Finance and Markets: This is the second version of blockchain, its application is banking and financial processing: expanding the scale of Blockchain, bringing blockchain integration into financial and marketing applications. school. Assets include stocks, checks, liabilities, ownership and anything related to a deal or contract.
- Blockchain 3.0 – Design and Operation Monitoring: Currently, this is the highest version of blockchain, with this version, Blockchain technology will cross the border only serving the financial sector, and enter the fields. Other fields like education, government, health and arts …
VII. Consensus mechanisms in Blockchain
The consensus mechanism in Blockchain can be understood as the way that people managing in the blockchain system can agree for a transaction to occur in the system. Here are the common types of consensus mechanisms in blockchain:
- Proof of Work: This is the most common consensus mechanism, used in Bitcoin, Ethereum, Litecoin, Dogecoin and most cryptocurrencies. This is a consensus mechanism that consumes quite a lot of power.
- Proof of Stake: This is a common consensus mechanism in Decred, Peercoin and in the future, Ethereum and many other cryptocurrencies. This consensus mechanism is more decentralized, consumes less energy, and is not easily threatened.
- Delegated Proof-of-Stake: This is a common consensus mechanism in Steemit, EOS, BitShares. This consensus mechanism has low transaction costs; extendable; High energy performance. However, it is still somewhat focused because this algorithm selects a trusted person to authorize.
- Proof of Authority: This is a common consensus mechanism commonly found in POA.Network, Ethereum Kovan testnet. This consensus mechanism has high efficiency, good scalability.
- Proof-of-Weight: This is a common consensus mechanism in Algorand, Filecoin. This consensus mechanism is customizable and scalable. However, the process of promoting development will be a big challenge.
- Byzantine Fault Tolerance: This is a common consensus mechanism in Hyperledger, Stellar, Dispatch, and Ripple. This consensus mechanism is highly productive; low cost; extendable. But still can not completely trust.
VIII. The application of blockchain in life
 Some industries that blockchain technology can impact are:
Some industries that blockchain technology can impact are:
Automotive Technology (Automotive)
Manufacturing
Technology, media and telecommunications (Tech, media & Telecommunications)
Financial services (Financial Services)
Art & Entertainment (Art & Recreation)
Healthcare (Healthcare)
Insurance
Retail
Public Sector
Real Estate
Agriculture
Mining
Transport and Logistics (Transport & Logistics)
Infrastructure construction (Utility)
IX. Reference:
https://en.wikipedia.org/wiki/Blockchain https://www.goldmansachs.com/insights/pages/blockchain/ https://www.binance.vision/en/blockchain
