Intel was visited by hackers, 20GB of source code and classified documents about the chip leaked on the internet
- Tram Ho
This morning, a developer named Tillie Kottmann revealed 20GB of extremely valuable data, including the source code and confidential documents of the chip giant Intel. This person said I received data from an anonymous hacker and it was leaked from a vulnerability in the Intel system.
According to Kottman, the majority of the documents are IP protected properties of Intel and have never been disclosed anywhere. Kottman named this data block “Exconfidential Lake” with the name Lake indicating it contained documents related to Intel’s 10nm chip family.
Several leaked images show that the leaked data block contains confidential information that is essential for Intel customers such as motherboard design, BIOS and other components to interact with the CPU and others. other chips are manufactured by Intel.
Much of these documentation and source code pertain to Intel’s chip platforms, including the Kaby Lake and Tiger Lake family, as well as other products, including the Intel sensor cluster developed for SpaceX.
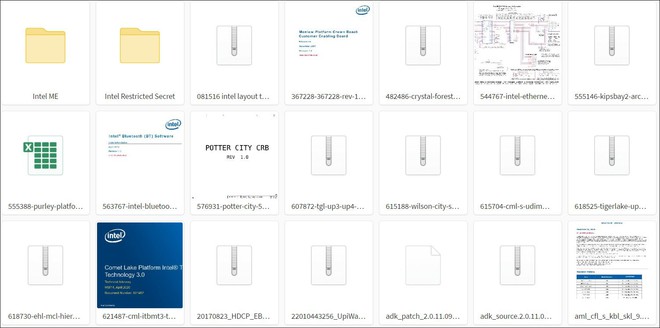
Screenshot of some leaked Intel documents
One of the other highlights of this data block is that it contains a document called “Whitley / Cedar Island Platform Message of the Weeks”, dating back to May 5. Cedar Island is the motherboard architecture located underneath the Cooper Lake and Ice Lake Xeon CPUs. Meanwhile, Whitley is a dual-socket architecture for both Cooper Lake (14nm) and Ice Lake (10nm) XEON CPUs.
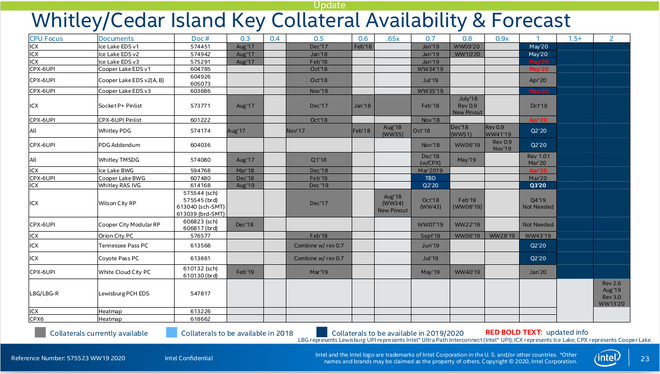
Some other documents in this data block also mention voltage errors in some Ice Lake chip models. It is not clear whether these errors occur on the entire line of chips shipped to customers or only on reference motherboards sent to customers by Intel.
How did this happen?
While Intel said it does not believe these documents could be stolen due to a vulnerability in the network, screenshots between Kottman and the hacker providing the other block of data show the opposite answer. .
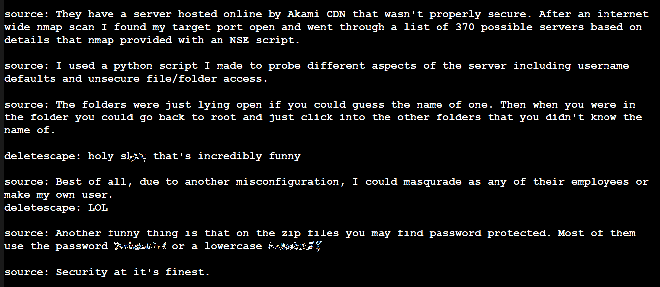
The screenshot shows the chat between Kottman and the hacker providing the above block of data
These documents are stored on an insecure server on Akamai’s Content Delivery Network (CDN), the hacker said. The hacker also claimed to have identified the server by using a network scanning tool to find the vulnerability and from there, with a piece of Python code, the hacker can guess the password of this block of data.
Significantly, in a chat with Kottman, the hacker said he could impersonate an Intel employee to access the data in this server, or even create his own user. Furthermore, some data files are protected with extremely weak passwords.
The hacker also said that the 20GB data block mentioned above is just the first part, and a lot more data will be revealed in the near future.
Refer to ArsTechnica
Source : Genk
