Hello everyone, the promise from “Stealing Cookies by taking advantage of XSS security errors” – Link until now has the opportunity to implement.
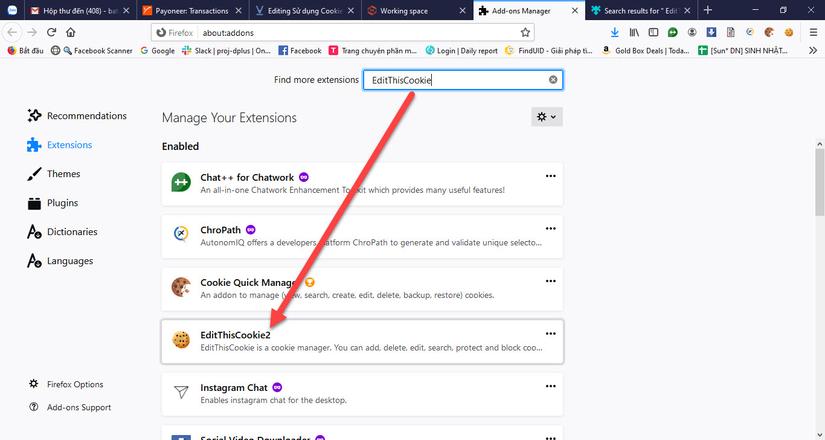
As in the previous article, we took advantage of the XSS security hole to steal Cookies, so after we have Cookies, what can we do ??? In this article, I will guide you how to use Cookies to login account with the EditThisCookie tool (available on FF and Chrome, search immediately) ^^.
The implementation context is that the company is applying the idea to answer a few questions about 7 Core Values in order to be logged in …. so sad and skinny (maybe I can get anywhere> “<), and the idea is Using Cookies to login will save you from having to answer questions (ahihi).
A. Search for WSM Cookies
In the past, when WSM was still corn, XSS holes were full, it was stolen, after several errors, it also patched a bunch, maybe left somewhere that I have not found yet, let’s go get the main Cookie by using the traditional way: v You need a tool to send API requests, use Jmeter ^^
Let’s research API to send to get any Cookie:
- Homepage: https://wsm.sun-asterisk.vn/ >>> send this to get CSRFToken
- Random questions: https://fitm.sun-asterisk.vn//core_values/questions/random_question?language=en >>> send this to get questions about 7 core values
- Valid answer: https://fitm.sun-asterisk.vn//core_values/questions/valid_answer >>> have questions in 2 then send this to submit answers
- GetCookie: https://wsm.sun-asterisk.vn/en/users/sign_in >>> If the answer is 3, then 4 will sign_in succeed, we will get the necessary Cookie.



Regarding the sending methods of requests, the Config elements, and the Parameters needed to send requests, you can get when the Inspect Element (F12) browser when making sign_in wsm. Now I will guide the creation of a plan running on the Jmeter tool, reviewing Jmeter knowledge and getting Cookies, a couple of jobs ^^
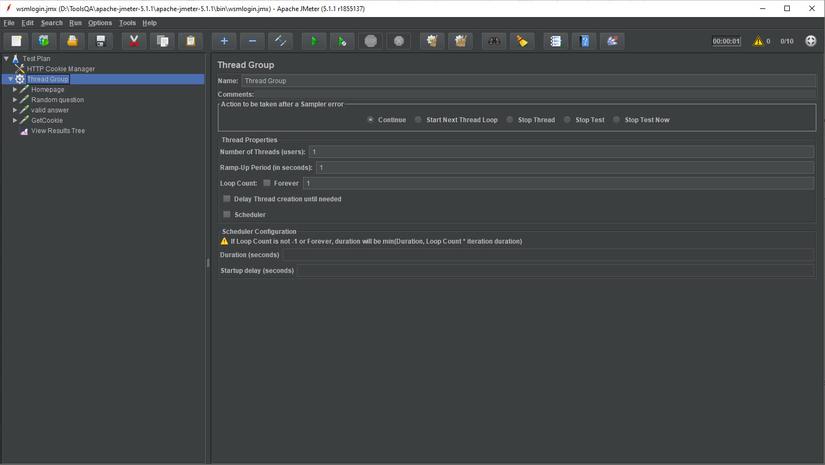
Test plan structure as above, first I add HTTP Cookie Manager to manage Cookies of the entire Test plan, then create a Thread group with the requests listed above, respectively: 1. Homepage -> 2. Random questions -> 3. Valid answer -> 4. GetCookie
- Homepage: Method GET https://wsm.sun-asterisk.vn/
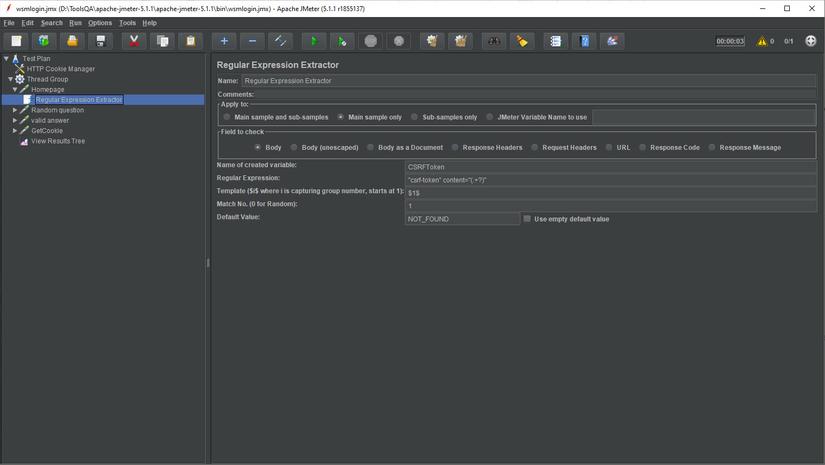
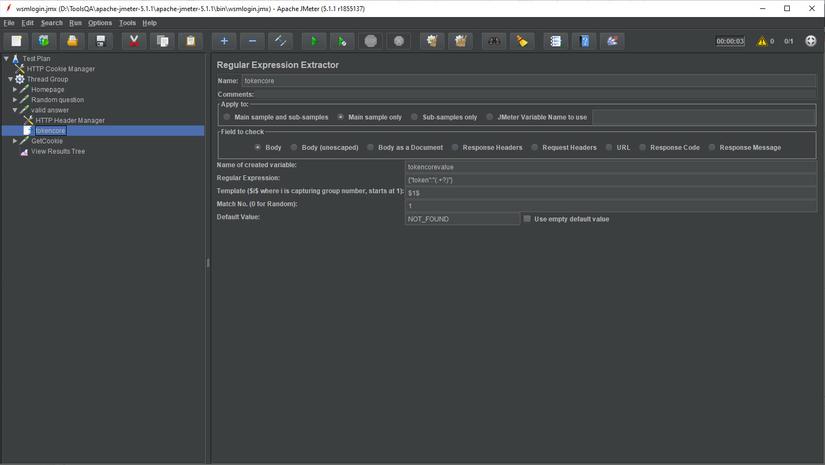
This request has no param, after calling, the response will have CSRFToken, I create Regular Expression Extractor to get CSRFToken as shown below.
- Random questions: Method GET https://fitm.sun-asterisk.vn//core_values/questions/random_question?language=en
This request also has no param, after calling, in the response will have questions about 7 core values and the options of the answer, I created Regular Expression Extractor to get questions and answers only. Note, the question has 1 token of the question but the answer has up to 4 tokens, I just need to get the first sentence is enough, regardless of whether the first answer is right or wrong. 
question_token 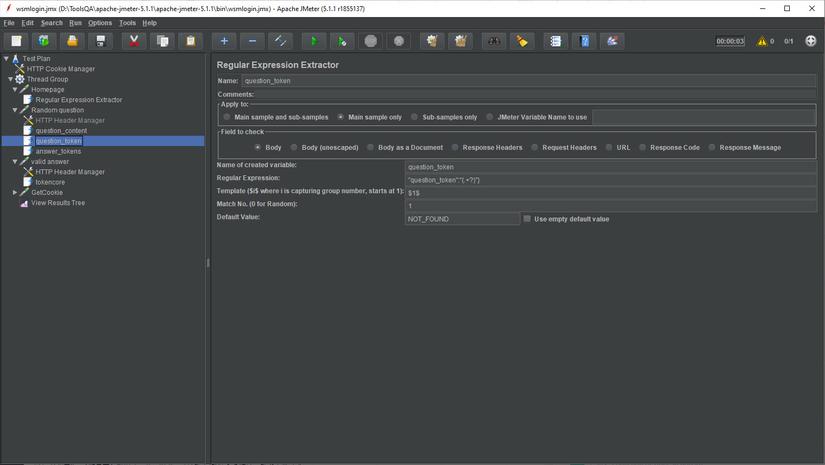
answer_tokens 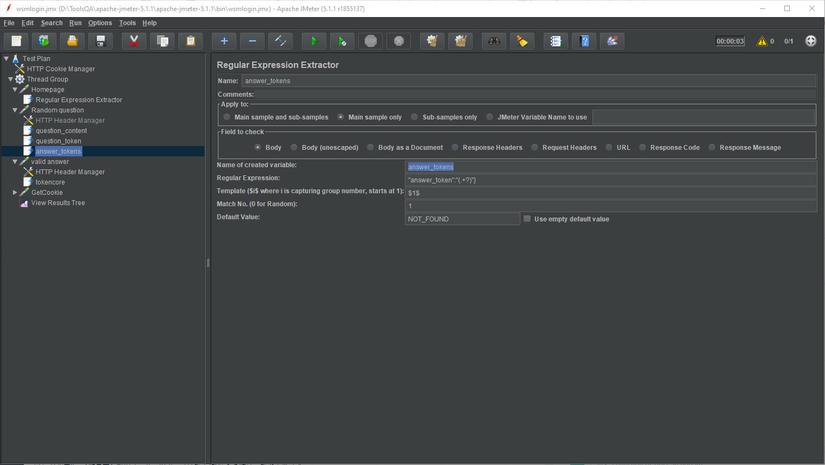
- Valid answer Method POST https://fitm.sun-asterisk.vn//core_values/questions/valid_answer
This request needs Request Heades as below:
1 2 3 4 5 6 7 8 9 10 11 12 | Connection: keep-alive Host: fitm.sun-asterisk.vn User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:71.0) Gecko/20100101 Firefox/71.0 Accept: application/json, text/javascript, */*; q=0.01 Accept-Language: en-GB,en;q=0.5 Accept-Encoding: gzip, deflate, br Content-Type: multipart/form-data; boundary=---------------------------213946871895 Origin: https://wsm.sun-asterisk.vn Connection: keep-alive Referer: https://wsm.sun-asterisk.vn/en Content-Length: 457 |
Parameters passed are the questions_token and answer_tokens that we get in 2. Random questions, you pay attention to call variables $ {question_token} and $ {answer_tokens} okay:
1 2 3 4 5 6 7 8 9 10 | -----------------------------213946871895 Content-Disposition: form-data; name="question_token" ${question_token} -----------------------------213946871895 Content-Disposition: form-data; name="answer_tokens[]" ${answer_tokens} -----------------------------213946871895-- |
After sending the request successfully, there will be 1 result token in the response, this result can be true or false, just get the token and then calculate:
- GetCookie Method POST https://wsm.sun-asterisk.vn/en/users/sign_in
This request needs Request Heades as below, here you need to pass the CSRFToken retrieved in 1. Homepage, pay attention to call back $ {CSRFToken}:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 | Connection: keep-alive Host: wsm.sun-asterisk.vn User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:71.0) Gecko/20100101 Firefox/71.0 Accept: application/json, text/javascript, */*; q=0.01 Accept-Language: en-GB,en;q=0.5 Accept-Encoding: gzip, deflate, br X-CSRF-Token: ${CSRFToken} Content-Type: application/x-www-form-urlencoded; charset=UTF-8 X-Requested-With: XMLHttpRequest Origin: https://wsm.sun-asterisk.vn Connection: keep-alive Referer: https://wsm.sun-asterisk.vn/en Content-Length: 486 |
The transmission parameter includes: authenticity_token: $ {CSRFToken} is already taken at 1. Homepage user [token_core_value]: is $ {tokencorevalue} retrieved at 3. Valid answer user [email]: is your email user [ password]: is your password
ahihi, cover carefully then 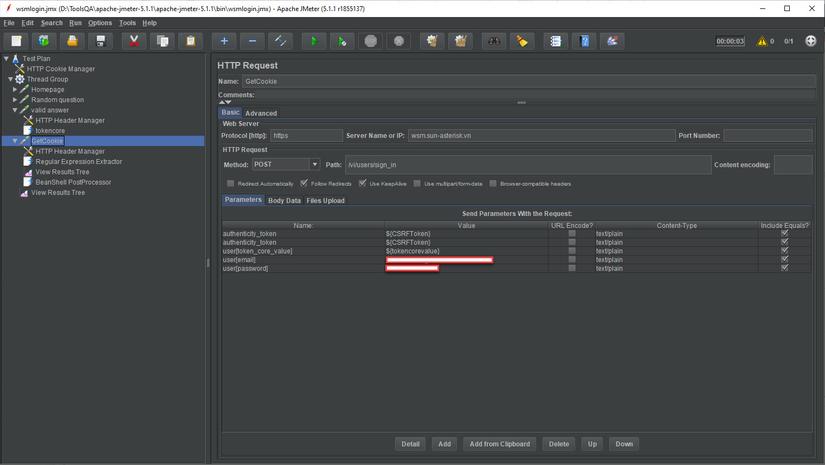
After sending the request successfully, there will be a Cookie in the response, this is the purpose I need to get:
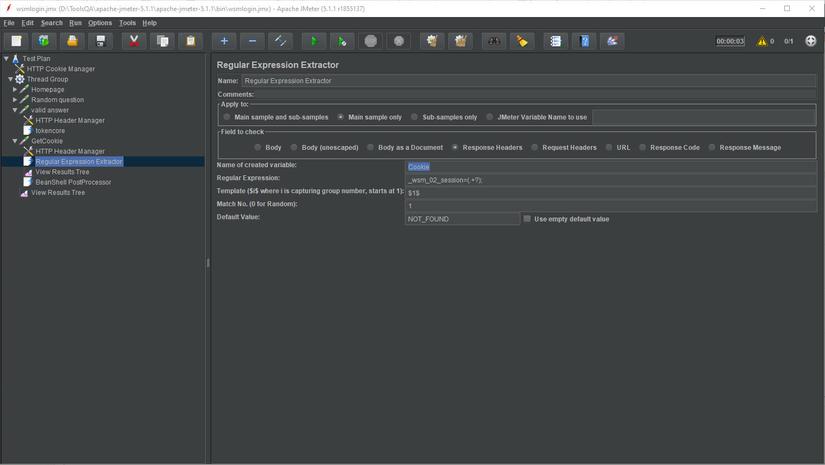
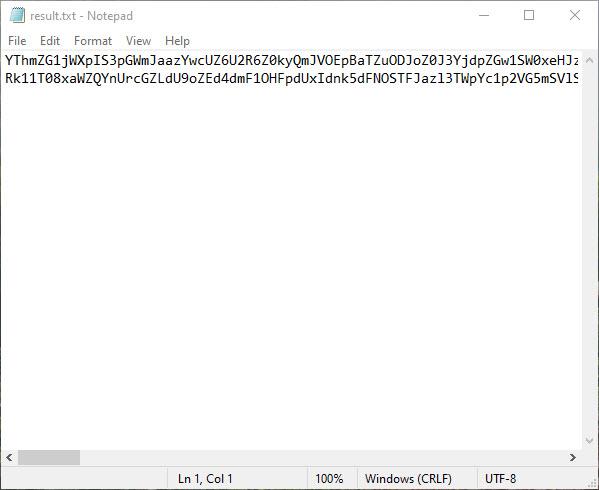
At this point, I need BeanShell PostProcessor to print Cookies into txt file, just a little colorful for fun, yes, no. ^^
1 2 3 4 5 6 7 8 9 10 11 12 13 14 | String cookie = vars.get("Cookie"); // get data from var Cookie String question = vars.get("question_content"); // get data from var question_content String answer = vars.get("answer_tokens"); // get data from var answer_tokens if (!cookie.equals("NOT_FOUND")) // điều kiện nếu tìm thấy cookie thì mới in kết quả response { f = new FileOutputStream("D://result.txt", true); //specify true if you want to overwrite file. Keep blank otherwise. p = new PrintStream(f); this.interpreter.setOut(p); print(cookie + "," + question + "," + answer); // in ra cookie + question + answer f.close(); } |
OK, the script will look like this:
User comes 1. Homepage, he receives 1 question 7 core value 2. Random questions, he submits the answer 3. Valid answer, then he will sign in, sign in successfully he will get 4. GetCookie ^^
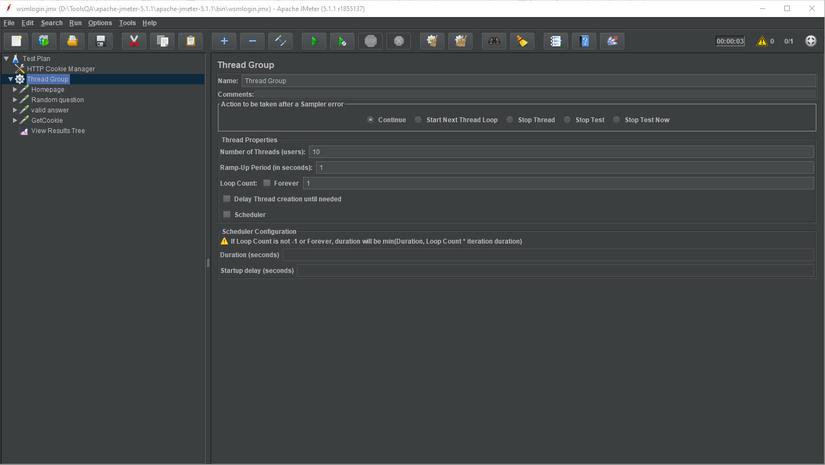
The problem is in step 3. Valid answer, we can not control whether the answer is true or false, the Test Plan we created above will receive a random question and get the first answer option. Tell right or wrong to submit. So to solve the problem, I ran a series of 10 consecutive times to receive random 10 pairs of questions / answers, just 1 pair returns the correct result, I will have Cookies and print out the text file for me.  Config thread group as shown below:
Config thread group as shown below:
Test play and see what results, grab 2 Cookie lun ^^
B. Using Cookies of WSM to login and by pass question 7 core value
Actually, the step to get a new cookie is difficult, until this step, you only use the Tool, you search the EditThisCookie tool:
Copy the Cookie obtained above, go to the WSM homepage and paste the Cookie into the EditThisCookie tool, then click Save:
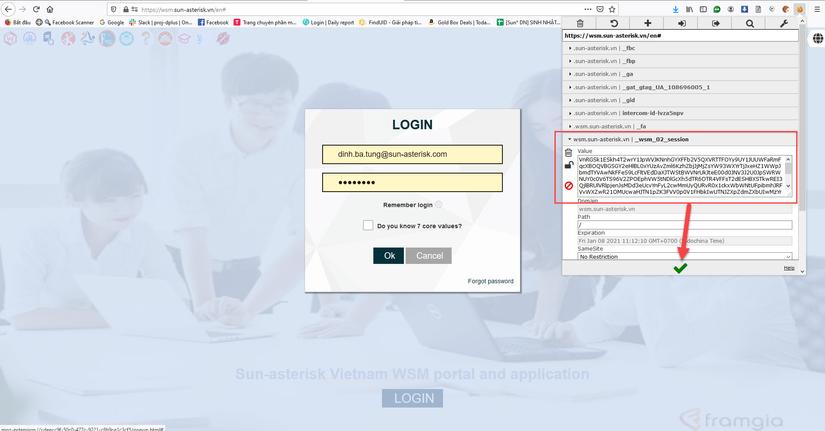
F5 plays to see the miracle, you have successfully signed in WSM with the obtained Cookie, demo clip:
Here let me end the article, hoping that you can see the dangers of XSS security.

