In the previous section, we have come together to learn about the Encoding / Decoding process during the transmission process on the Internet, in this section we will together learn about Same Origin Policy and Cookies.
What is Same Origin Policy?
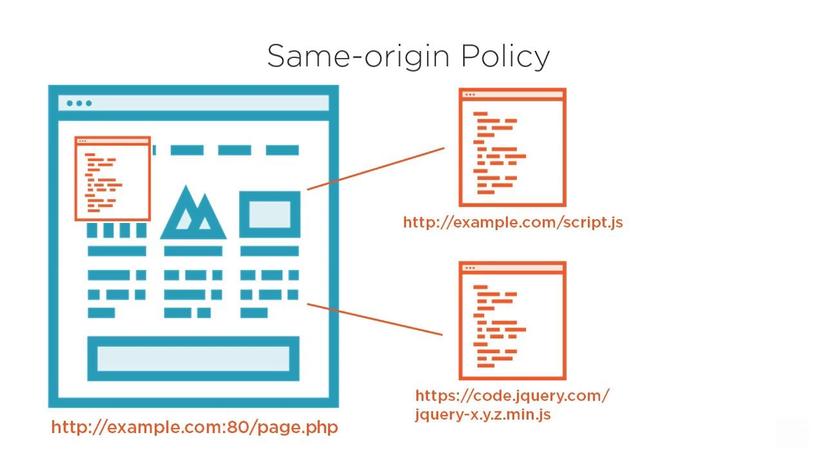
Same-origin policy (SOP) is one of the most important security policies on modern browsers, which prevents JavaScript code from making requests to sources other than the source from which it is returned. The three main criteria for comparing requests are:
- Domain (domain name)
- Protocol
- Port (connection port)
Simply put, a request will be considered valid only if it meets the above 3 criteria (same domain, same protocol and same port).
Example
Imagine when we are opening 2 tabs, 1 tab is facebook, the other tab is 1 certain website that contains malicious code. It is very dangerous if the scripts on the tab side of malicious code can freely manipulate on the facebook tab on the other side, and SOP was born with the task of preventing these actions.
Here is an example of site origin’s SOP violation list ( http://www.example.com ):
- http://www.example.co.uk (different domain)
- http://example.org (different domain)
- https://example.com (different protocol)
- http://example.com:8080 (other port)
Bypass Same-Origin Policy
Although the security advantages of SOP are obvious, in some cases this makes it difficult for developers.
Typically Internet Explorer has two exceptions that can be ignored SOP :
- If two domains belong to the same trust zone
- Excluding ports, ie with IE, http://company.com:81/index.html and http://company.com/index.html are the same source.
If a company has many web applications that require authentication in one place, for example, http://store.company.com needs to authenticate at http://login.company.com first. Receiving the data returned from the request to http://login.company.com is not possible because it has been blocked due to SOP violations.
We have many ways to solve this situation, the most commonly used is Cross Origin Resource Sharing (CORS). However, we will talk about CORS in another part.
What is a Cookie?

The simplest explanation is: A cookie is a temporary file that is automatically created on your computer, every time a user accesses a website, it will store personal information such as a user account. Enter, setup options … to use for future visits.
A more professional definition: A cookie is an encrypted file containing the user’s information, created by the website and stored on the user’s own device (pc, laptop, smartphone …..) . When the browser makes a request to the server, the information stored in it will be attached by the browser and sent back to the server.
Because Cookies are created by the website that a user accesses, 2 different websites (even if they are on the same server) will have 2 different Cookies sent to the server. In addition, each browser has its own method of managing and storing Cookies , so two browsers accessing the same website will receive 2 different Cookies.
Types of Cookies
Cookies can be classified into two main categories:
- Session cookies : this cookie is retained in the browser and will be deleted when the browser is closed. When the new browser window is reopened, the user will have to provide his or her credentials again.
- Persistent cookies : this cookie is kept in the browser until it expires or is deleted manually. The website will remember the authentication even if the user closes the browser.
Cookie Contents
The main components of cookies include:
- Name – used to identify the name, not case sensitive.
- Value – values are stored in cookies
- Domain – is the domain that owns cookies
- Path – is the path specified, where cookies will be sent
- Expiration – the expiry date of cookies, after the specified time, cookies will be deleted
- Secure Flag – cookies will be sent only when flagged
Testing Cookies
Here are ways to test cookies:
- Disabling Cookies – we need to check the website after disabling cookies, to see if everything is working properly (can check access functions such as login logout, navigation bar, personal options). by the way, notice of need for cookies …)
- Corrupting Cookies – first we need to find out the location of the cookies to be searched, then manually edit the values inside and outside the cookies so that the cookie is no longer “clean”, then proceed to check once Website functionality uses cookies.
- Removing Cookies – Clear all cookies and conduct a website check change
- Cross-Browser Compatibility Test multiple browsers – check the performance of cookies on different browsers
- Editing Cookies – is similar to Corrupting Cookies but the difference is that it is lighter, we can change the personal information of the user stored in cookies to another person, then proceed to access the system system.
References :
