I) What is OSINT?
The first step in a targeted attack – or a red team test is Gathering the target's information. Then using OSINT is a fairly effective and convenient way to collect the information of the target.
So what is OSINT we are talking about? OSINT is an abbreviation for Open Source Intelligency. In which OS is Open Source, also known as open source is public on the internet and Intelligence is Intelligence (the collection of information). From this we can understand that these are the methods and ways to extract information from videos, images, documents, … from what is related to the goals that are available and public on the internet. These resources can be anywhere: on forums, on newspaper pages, in a book, video or open libraries, previous reports and histories.
II) Who can this article help?
- For sales people, marketing or product managers can use it to find potential target customers, help increase conversion rate – help increase the number of customers and more effectively when public publicize a product or service
- For a pentest and dev team, we can use it to gather information about the target to get an overview and have useful information to use during the exploitation process as well as for the dev party. understand and avoid exposing sensitive information to the internet.
III) Techniques when using OSINT and sources to extract information.
First, you may need to ask a few questions to yourself:
- What information are I looking for / what / what?
- My main goal is to get what?
- Who / what will be his goal?
- We arrange and do things to ensure the effectiveness and complete necessary information?
In addition, we can see that many of the OSINT techniques are being used by the government and the military that are targeting us, but some do well, but some do not, the problem is in part. OSINT strategy as you have to find out where the information from will be able to provide you with the exact closest to what you are looking for.
And here may be some criteria to target when finding information of an object:
- Use Google Maps and other open satellite image sources to retrieve images of a user's geographic location.
- Monitor personal and business blogs, as well as review user activity on forums
- Review content available on social networks like Facebook, Twitter, Google Plus or Linkedin.
- Collect the full names of employees, job roles, as well as the software they use.
- Run port scans based on the target company's server infrastructure to find services running.
- Explore DNS Services, as well as domain names, subdomains and IP addresses with the SecurityTrails toolkit.
- Use tools to search for internet-connected devices like Shodan used by your target.
- Use people's data collection tools like Pipl , who will help you reveal a lot of information about individuals in a single place.
- Access cached data from Google – often disclosing interesting information.
- Discover older versions of websites to reveal important information using the Wayback Machine
- Identify mobile numbers, as well as mailing addresses from social networks or Google results.
- Search for photos and videos on popular social photo sharing sites, like Flickr, Google Photos, etc.
- Identify all social networks used by the target user or company.
- Use tools like GeoCreepy to track geolocation information to get a clear picture of the user's current location.
- Use automated OSINT tools to retrieve information, such as Spiderfoot or Us
To the last step is to summarize all the information you have just found, filter and categorize them and system to get the most comprehensive look.
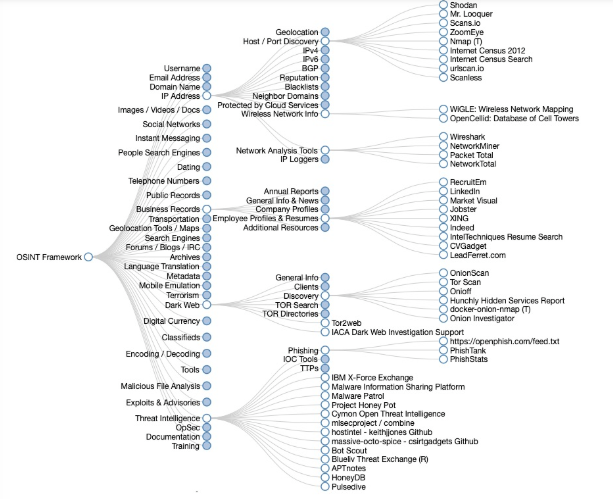
OSINT Framework
A good place to start is the OSINT Framework , a framework created by Justin Nordine. This framework provides links to groups of resources for a variety of tasks from collecting email addresses to social media search or deepweb.
In many articles about OSINT tools, you'll see references to one or two packages included in the Kali Linux distribution, like Harvester or Maltego, but for a full overview of OSINT tools available for Kali, See the list of Potassium Tools and examples of how to use each tool.
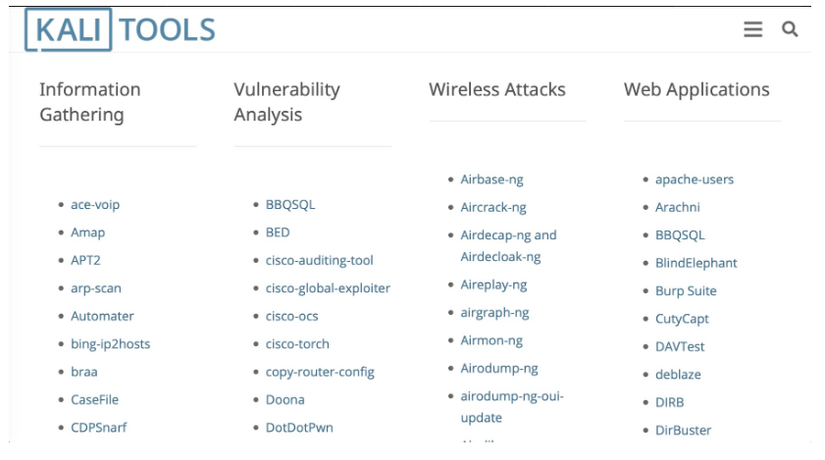
Among the useful tools you'll find here for collecting open source information are favorite researchers like Nmap and Recon-ng. The Nmap tool allows you to determine the IP, speak and determine which server is available, which service that server provides, the operating system they run, what firewall they are using, and more.
In addition, Recon-Ng is a tool written in Python by Tim Tomes for detecting. You can use it for things like listing subdomains, but there are dozens of modules that allow you to connect to things like internet search engines Shodan, Github, Jigsaw, Virustotal and others. .
