I. What is 3Box?

3Box is a secure and decentralized user data storage system. It’s the easiest way for developers to build apps without having to worry about back-end to manage user data.
II. Why should you use 3Box?
First we will find out why 3Box is the best way for developers to store and manage user data for the following reasons:
 Build a fully featured application with less back-end infrastructure :
Build a fully featured application with less back-end infrastructure :
Firstly, 3Box allows front-end developers to store user data on an open storage network instead of centralized database server, browser localStorage or blockchain.
This allows 3Box developers to develop applications that both provide a good user experience like web2 but ensure user data is distributed like web3.
 Develop faster and easier with the tools and APIs available :
Develop faster and easier with the tools and APIs available :
Besides, 3Box provides developers a set of tools to quickly build a complete application with the ability to expand when the number of users increases. The 3Box APIs support functions including identity, auth, profiles, storage, and messaging. You can learn more about the 3Box API and SDK here .
 Decentralized data is stored on IPFS and OrbitDB:
Decentralized data is stored on IPFS and OrbitDB:
3Box is a distributed data storage system using IPFS for decentralized storage, OrbitDB for database structure along with 3ID for decentralized identification.
To ensure 3Box is able to maintain usage on these new technologies, the developer of 3Box also provides additional cloud infrastructure to improve the reliability and performance of decentralized networks. This includes hosted nodes, data pinning services and caching layers.
 Improve the security and privacy of user data :
Improve the security and privacy of user data :
The decentralized architecture of 3Box allows developers to eliminate most of the work related to the security and protection of user data on their servers.
3Box can do this because data is stored directly with users, it also gives users more privacy and control over how their personal information is shared and used by online applications.
When data is stored privately on 3Box, applications and other users cannot read it unless the user grants them explicit permission. Users have full discretion in sharing their personal data. It is difficult to happen in a centralized application.
 Support for mobility and data interoperability :
Support for mobility and data interoperability :
One of the biggest benefits to 3Box is when stored data is tied to users, making it easy for users to bring their data across different applications, networks and services without having to recreate it. New data each time you switch to a new application.
In addition, user data on 3Box belongs to the user, not to any form of provider lock, including 3Box itself, because users can always take their data to another provider. same standards.
 Users do not need to install new software
Users do not need to install new software
Simply because the features of the 3Box are provided via the Javascript SDK, users will not need to install any additional software to be able to experience the features of 3Box.
III. Architecture of 3Box
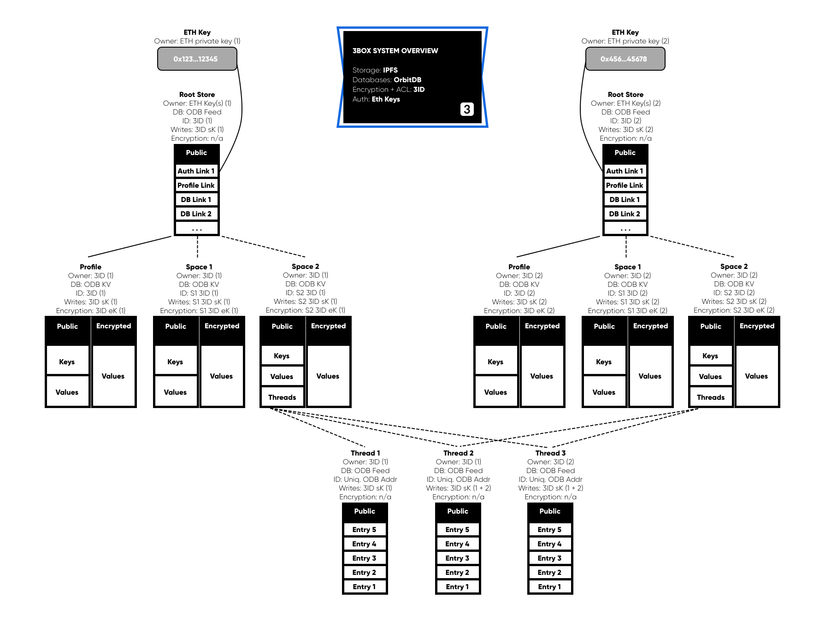
Next we go to learn and have an overview of the architecture of 3Box. There are 4 layers of 3Box user data management system, including:
- Wallets
- 3ID Data Identity Protocol
- OrbitDB Databases
- IPFS Storage
Now we will explore in detail each layer above.
Wallet: Key Management and Authentication
In 3Box, the wallet plays the role of storing the user’s private key as well as using that key to authenticate access and manipulate data via 3ID (we will talk about 3ID below).
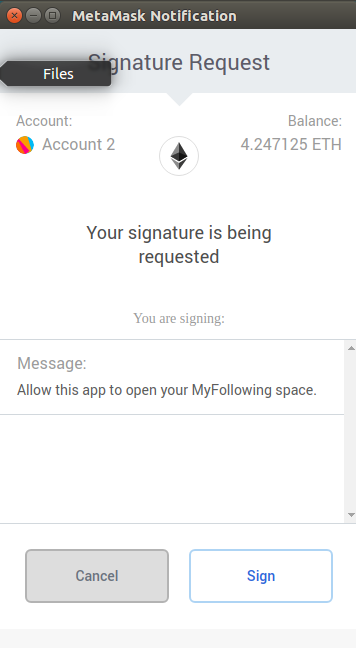
Data Authentication:
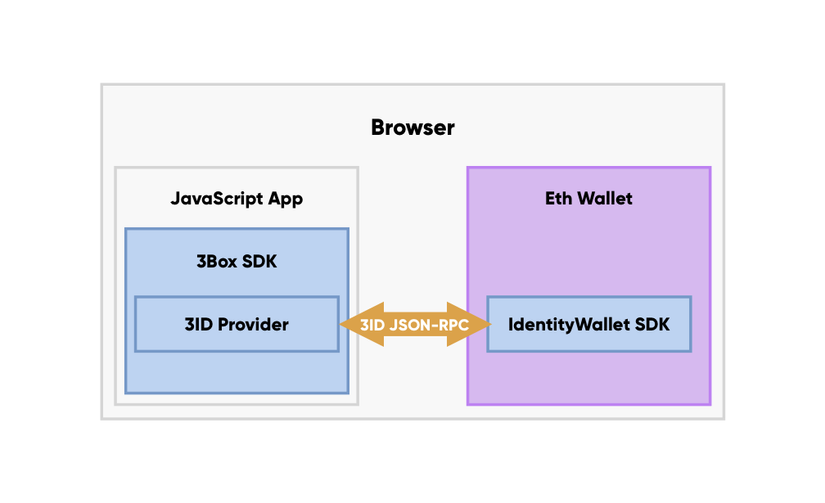
There are 2 ways the wallet can authenticate the database via 3Box.
- EthereumProvider : Basically, the Ethereum wallet can support 3ID database authentication through the
Personal_signmethod in the EthereumProvider API.
When applications call openBox () or openSpace () in API 3Box to gain access to the user’s database, the request is transferred via the Ethereum JSON-RPC interface to the wallet where the personal_sign request will be displayed. for users.
If this request is approved, the message is signed with the Ethereum private key and the results are returned to the application via Ethereum JSON-RPC. The combination of a private key and a message is used to generate 3ID and additional database keys, which are then stored in localStorage and used by the application to perform database operations.
- 3IDProvider:: The other way an Ethereum wallet can support 3ID database
authenticateis theauthenticatemethod in the standard 3IDProvider API.
When applications call openBox () or openSpace () in API 3Box to gain access to the user’s database, this request is passed via the 3ID JSON-RPC to the wallet where the authenticate called and the request is displayed. for users.
If this request is approved, the message is signed with the user’s Ethereum private key and the results are kept inside the wallet and used to generate the 3ID and additional database keys used to execute it. manipulation with database.
In addition, 3IDProvider allows wallets to link multiple blockchain key pair accounts with the same 3ID, in addition to improving UX with automatic signature rights (users can allow wallets to automatically approve facility requests). data).
Below is a list of some of the most popular EthereumProvider JavaScript libraries for applications: Web3.js, Ethers.js and Web3Connect.js.
And here is a list of some of the most popular Ethereum wallet providers for users: MetaMask, Portis, Fortmatic, Authereum, Universal Login and WalletConnect (support for Gnosis Safe, Argent, Rainbow and other mobile wallets).
3ID: Data identification, Access control, Encryption
3ID is a decentralized identity protocol (DID), which provides data identification, access control and encryption for user data stored on decentralized web in decentralized databases or IPFS. .
Data Identity
At the core of each 3Box account is the 3ID, decentralized identification number (DID), which acts as a unique data identifier and allows users to manage their data and information on databases. , different decentralized accounts and networks.
did: 3: bafydfhqlwaedhflasdhfqkawhfalwhsfqjawdfhw
All user related data and all messages and contact information sent from the user, are controlled by their 3ID.
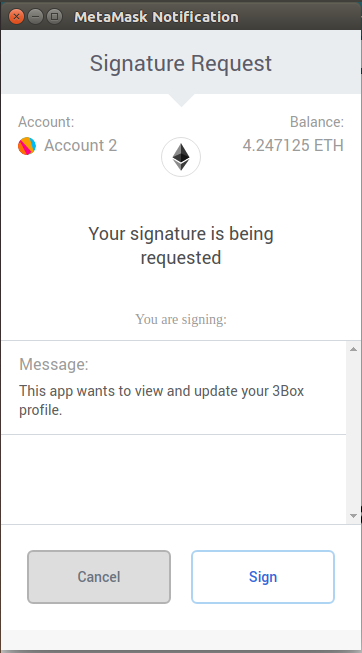
Create or validate using 3ID
As mentioned above, the 3ID is generated in a determined manner by combining the user’s private key and the 3ID consent message.
“This app requests to view and update your 3Box profile.”
When users approve this message by signing it, they will create their 3ID. The application can request this function by calling the openBox () available in the 3Box API. If the user does not yet have 3ID, a user will be created and initialized for them. A link will also be added to the 3ID’s original repository so others can verify this link. If the user already has 3ID, it will simply be initialized.
Additional public key can then be added to the 3ID, allowing users to authenticate the 3ID and additional databases with different private keys and linking their data across multiple accounts. Wallets can link multiple key pairs and accounts with the same 3ID using the addAuthMethod () in API 3IDProvider.
Creating a database key (Creating Database Keys)
When the user approves a consent message in their wallet to create a 3ID, additional database authorization keys are taken from the user’s 3ID, including: signing key (sK) to sign all updates. database; and the encryption key (eK) to encrypt and decrypt data for that database.
With EthereumProvider Wallet integration, these database keys are kept in localStorage for the duration of the user’s application session. This means that users only need to approve the consent message once, but can then perform unlimited operations on the approved database using these keys.
With the integrated 3IDProvider wallet , these database keys are kept inside the wallet for a period of time decided by the wallet. The wallet can choose to display a confirmation for every request made by the application or automatically sign all requests on behalf of the user.
Data access control (Data Access Control)
3ID allows a single user to coordinate and control multiple decentralized databases, each with its own access control. Although traditional server-based systems have separate encryption and access control concepts, 3ID uses the Cryptographic Access Control (CAC) model using signatures (sK) and encryption (eK) to create a server-less data access control system.
3Box uses the CAC of 3ID because the data on the 3Box is stored on an open IPFS network and is not kept server-side, so access control must be done in a way without a server.
Get public data (Fetching Public Data) :
Data stored publicly in databases on the 3Box network is stored in plaintext. The data is signed by sK but not encrypted by eK , so this data is available for others to use without any access control approval from the user.
Participants can find all public data from the user’s root store, profile, space or database using any method of retrieving data from the 3Box REST API.
Performing data operations (Performing Operations on Data) :
With 3ID, all data operations occur on the client side after the user has authenticated a specific database.
All database operations such as writes, updates, and messages must be signed by the 3K sK ; in addition, private data must be encrypted / decoded symmetrically by eK of 3ID.
As mentioned before, depending on the wallet’s 3ID integration, these keys may exist in localStorage in the user’s browser or inside the wallet.
This means that apps and services want to interact with users’ 3Boxs in ways other than reading public data, such as writing data, encrypting / decoding data, or deleting data, authentication will be required from the user’s wallet via the consent message to create the sK signature key and eK encryption key required to perform these actions.
Access database profile :
Access control is specific to each user-controlled database, so applications need to request separate permissions for specific databases, including user profile and their space . .
Applications that want to access a user’s 3Box databse profile to update, decode, or delete data require authentication of the basic 3ID consent message by calling openBox () in API 3Box.
“This app requests to view and update your 3Box profile.”
This is the message that will create or initialize the user’s 3ID and generate the signing and encryption keys, meaning that simply authenticating the user with your application, you can read and / or update the database. file.
Accessing Space / Thread Database
Applications that want to access the Space database (or the Thread Database included in it) to update, decode, or delete data must request Space 3ID consent message by calling openSpace () in API 3Box.
This is different from the consent for the profile (“This app requests to view and update your 3Box profile.”) And when approved will generate a completely different 3ID and then a signing key (sK) and different encryption key (eK). This is how 3IDs can access control of each database separately and allow selective disclosure.
Data encrypt
When applications want to store private data inside the database, a series of actions occur from the database’s eK to the symmetric encrypted key-value pair.
Each database has a unique 3ID and therefore, private access is controlled with a different eK. This is how the data is encrypted:
- When the user signs the consent of database access,
sK,eKandsalt(the data series is randomly generated) taken from 3ID - The key (PLAIN_KEY) and the value are chained together and added so that the length is a multiple of 24.
- The output of step 2 is encrypted with
eKusing theweetnacl secretboxto get the cipher value - Calculate the key by getting the hash function (PLAIN_KEY | salt)
- Store the
key-valuepair, with the key from step 4 and the cipher value from step 3
OrbitDB: Peer to Peer Databases

3Box data is stored in different OrbitDB database instances.
OrbitDB is a peer-to-peer, distributed, and peer-to-peer database. 3Box uses the Javascript implementation of OrbitDB, works both in Browserst and Node.js.
OrbitDB uses IPFS as data storage and IPFS Pubub to automatically synchronize the database with peers. Finally, this is a consistent database that uses CRDT to consolidate the conflict database, making OrbitDB a great choice for decentralized applications (dApps), blockchain applications and applications. Offline web application.
Database Types
OrbitDB provides many types of databases for different data models and use cases. At this time, 3Box uses the following types:
- Keyvalue : key-value database.
- Feed : a log may vary. Items can be added and removed. Especially useful for “shopping cart” use cases or blog posts or “tweets”
In 3Box,
key-valuestorage is used forspacewhilefeedis used forthread.
IPFS: Peer to Peer File Storage
Because 3Box is a system for managing user data on the decentralized web, IPFS – a peer-to-peer file storage network is used in 3Box.
About IPFS
IPFS ( The InterPlanetary File System ) is a peer-to-peer content identification system. IPFS provides data that enables the creation of fully distributed applications aimed at making the web faster, safer, and more open.
IPFS is a distributed file system that seeks to connect all computing devices to the same file system. This is similar to the original purpose of the Web, but IPFS is actually more like a swarm bittorrent.
Data routing
Data objects in IPFS are content-addressed (represented by many hash functions of the content, also known as content identifiers (CID)) instead of location addresses (http) as data in web architecture. http traditional.
If the content of an object changes, the object receives a new address. Participants only need to request the content search network and the network will perform appropriate routing to find and return content, regardless of which node is holding information. This reduces the reliance on centralized servers to store information, instead allowing for a completely open and open data distribution.
Data persistence
IPFS has developed a basic protocol for data retention, called Filecoin, that aims to ensure that data added to the IPFS network remains available to users as long as they receive some payment.
However, Filecoin is not yet suitable for commercial use. For this reason, 3Box operates a network of IPFS / OrbitDB pin node to ensure that 3Box data remains available.
Conclude
Hopefully through this article you can understand more about the architecture and how 3Box works. To experience more clearly about the features of 3Box, please refer here .
