In part 1 I introduced Level 1 – 8 of EVABSv4 lab. Through the first 8 levels we are familiar with ADB (logcat, shell, pull); SQLite DB Browser; A brief overview of the file structure in the apk file and the directory structure in the local storage of an application installed on an Android device.
In Part 2, I will talk more about using Frida framework, Patch app, Intercept http request by Burp Suite. I will not talk more about the content mentioned in the previous writeup. As for the knowledge about Frida and Burp Suite, I will guide you more.
And now we will continue with …
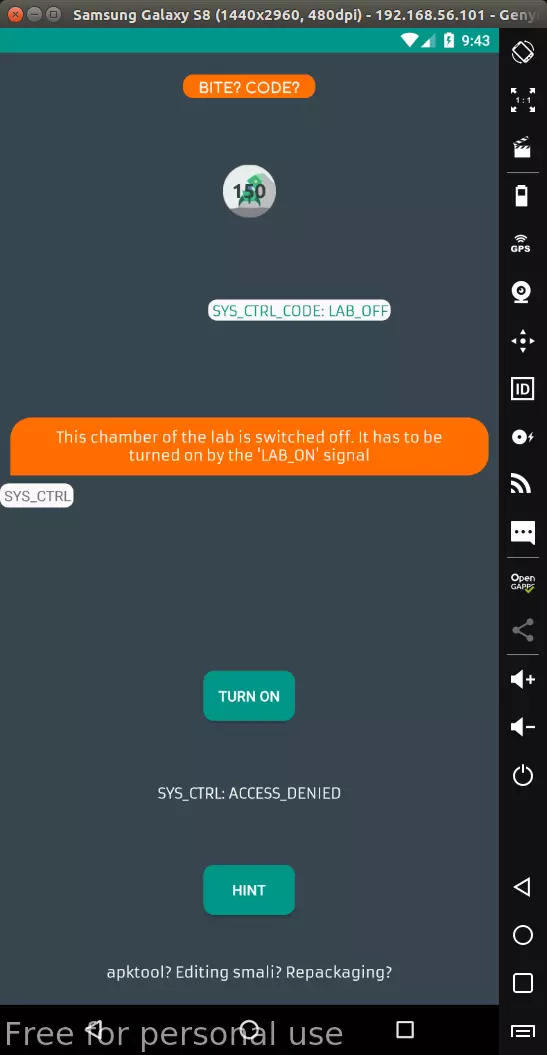
Level 9: Smali Injection
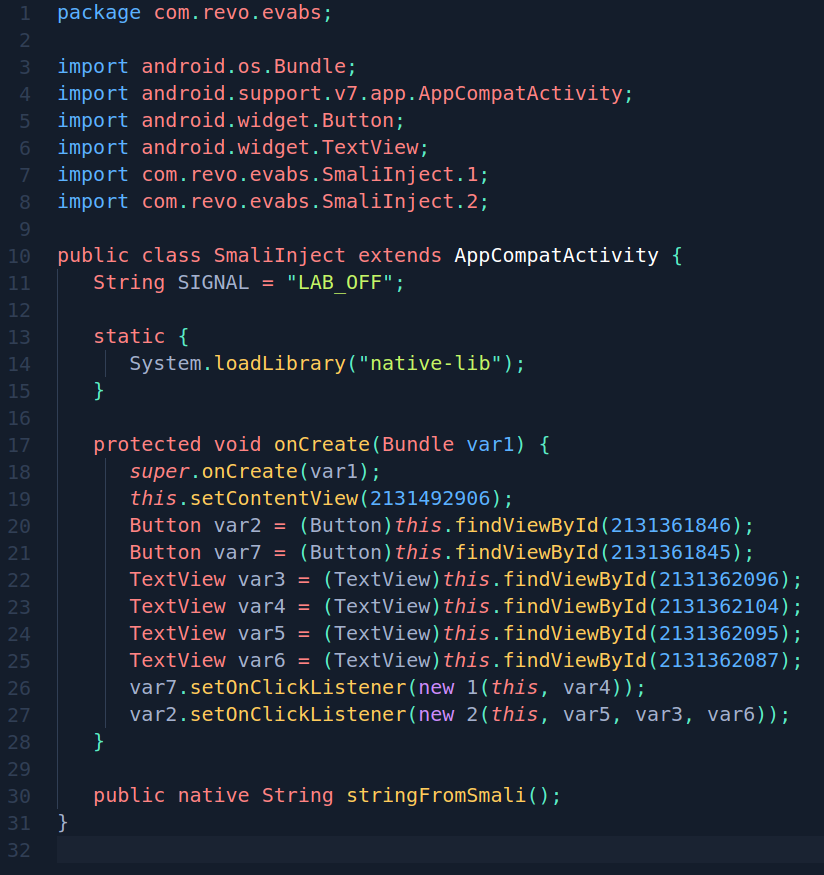
View source code by the bytecode viewer:
- SmaliInject.class:

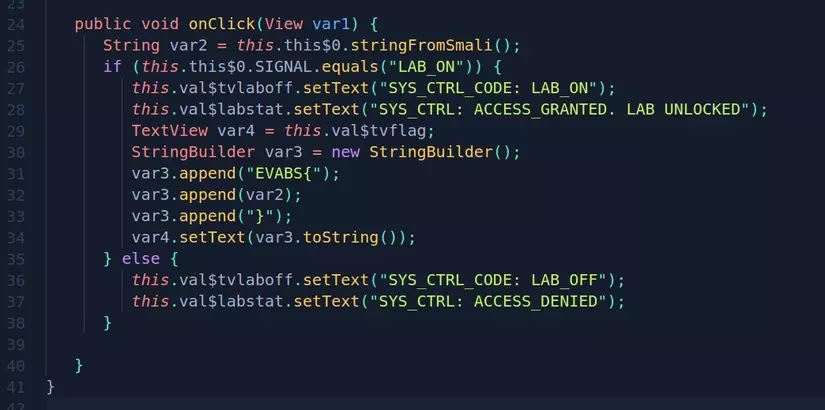
- SmaliInject $ 2.class:

It is easy to see if the variable SIGNAL = “LAB_ON” then the program will print the flag. But the SIGNAL variable is being set to default as “LAB_OFF” and no command will change the value of this variable.
So we need to fix smali code and rebuild the new app after fixing it, the chapter will print the flag. How to patch and rebuild apk file I mentioned in the article about [decompile and patch file apk]
We can edit the code and rebuild the new application and still use the normal functions because the Dev has no mechanism to check the code integrity.
Level 10: Intercept
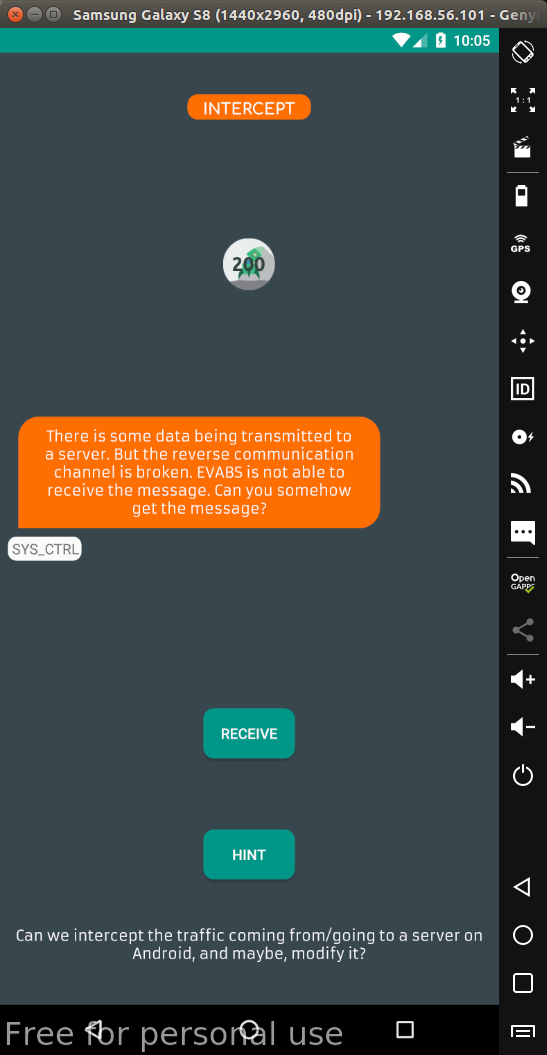
According to the hint, it is necessary to intercept the request with a burpsuite. In order for intercept to be requested on Android versions from Android N and above, a short root CA must be added. If you want to be simpler, just install EVABSv4 on devices with a version lower than Android N to use the CA burp.
How to install Burp Suite according to portswigger instructions .
Configure Proxy as follows to catch requests from Android devices out:
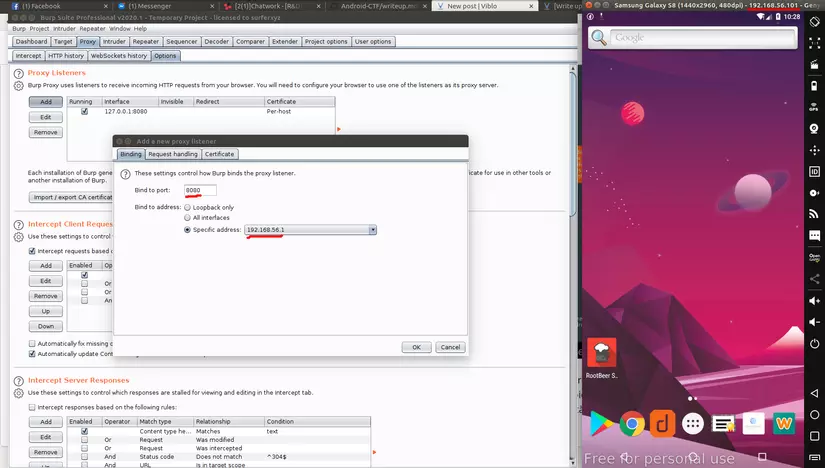
After config to intercept the request already, just Send to repeater and send the request. In respond contains flag.
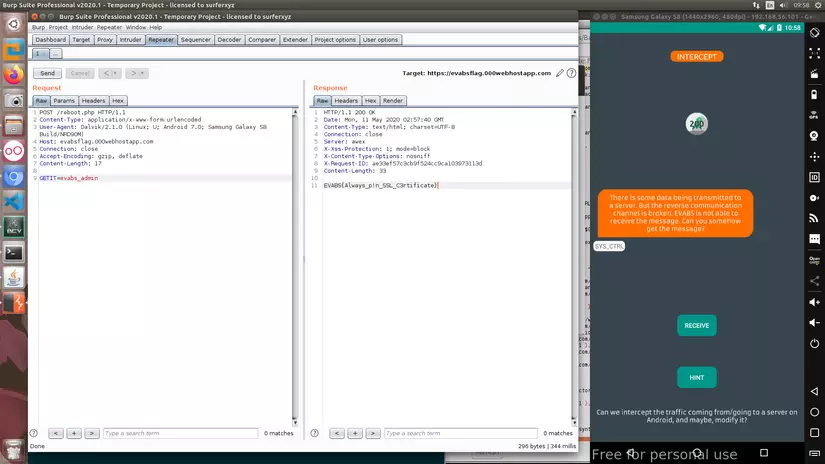
This is a risk of android app insecurity due to Dev not implementing SSL Pinning. If an application uses SSL Pinning carefully, the server will not respond to requests we send through Burp.
Level 11: Custom PERM
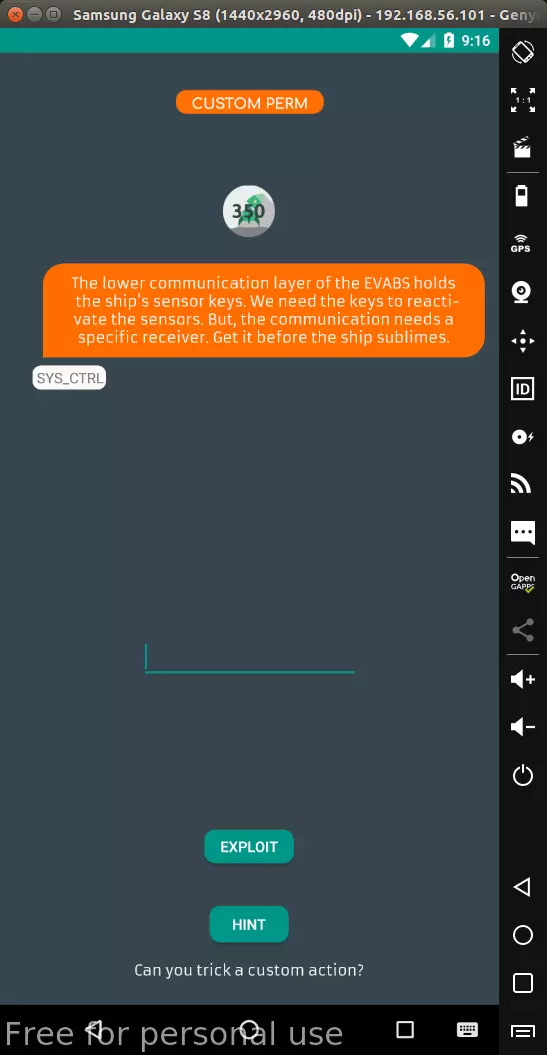
At this level we have to find the correct input, watching the source on the bytecode viewer can easily see that the correct input is cust0m_p3rm.
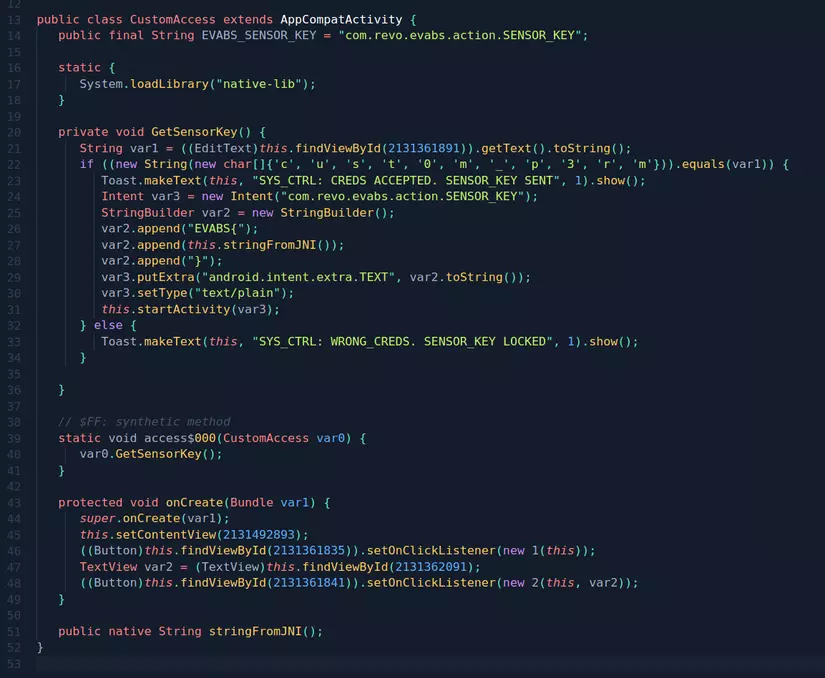
After entering the correct input, the flag will be passed to the intent com.revo.evabs.action.SENSOR_KEY with the putExtra () function.
Initially I found a way to influence the intent to get the data to intend to intend to transfer but it took a lot of time but failed. Maybe because my knowledge is not enough. So I switched to using Frida. The idea is to hook and fix the putExtra () function so it prints a flag.
I wrote a writeup post using Frida to hook the function here . This time I will explain more about Frida.
Understand roughly, when using Frida I will have to specify the object (function) that I want to change and the process (application) will implement this function. Frida will replace the content of the function you want with the new content. That way, when the application runs this function, it actually works the way we want.
There are 2 functions that I often use with Frida:
- Java.choose (): scan on the heap to find instance of the big class you want. Once found, Frida will run our new code.
- Java.use (): when the system creates a new instance of the class I want, the new code I write will be overwritten.
I often use Java.use () more. In this article, because the putExtra () function has many copies depending on the type of parameter, so I have to use overload () to indicate that the correct putExtra () function takes a 2 string parameter.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 | <span class="token keyword">import</span> frida <span class="token keyword">import</span> sys <span class="token keyword">def</span> <span class="token function">onMessage</span> <span class="token punctuation">(</span> message <span class="token punctuation">,</span> data <span class="token punctuation">)</span> <span class="token punctuation">:</span> <span class="token keyword">print</span> <span class="token punctuation">(</span> message <span class="token punctuation">)</span> package <span class="token operator">=</span> <span class="token string">"com.revo.evabs"</span> jscode <span class="token operator">=</span> <span class="token triple-quoted-string string">""" Java.perform(function () { send("[-] Starting hooks android.content.Intent.putExtra"); var intent = Java.use("android.content.Intent"); intent.putExtra.overload("java.lang.String", "java.lang.String").implementation = function(var_1, var_2) { send("[+] Flag: " + var_2); }; }); """</span> process <span class="token operator">=</span> frida <span class="token punctuation">.</span> get_usb_device <span class="token punctuation">(</span> <span class="token punctuation">)</span> <span class="token punctuation">.</span> attach <span class="token punctuation">(</span> package <span class="token punctuation">)</span> script <span class="token operator">=</span> process <span class="token punctuation">.</span> create_script <span class="token punctuation">(</span> jscode <span class="token punctuation">)</span> script <span class="token punctuation">.</span> on <span class="token punctuation">(</span> <span class="token string">"message"</span> <span class="token punctuation">,</span> onMessage <span class="token punctuation">)</span> <span class="token keyword">print</span> <span class="token punctuation">(</span> <span class="token string">"[*] Hooking"</span> <span class="token punctuation">,</span> package <span class="token punctuation">)</span> script <span class="token punctuation">.</span> load <span class="token punctuation">(</span> <span class="token punctuation">)</span> sys <span class="token punctuation">.</span> stdin <span class="token punctuation">.</span> read <span class="token punctuation">(</span> <span class="token punctuation">)</span> |
The results:
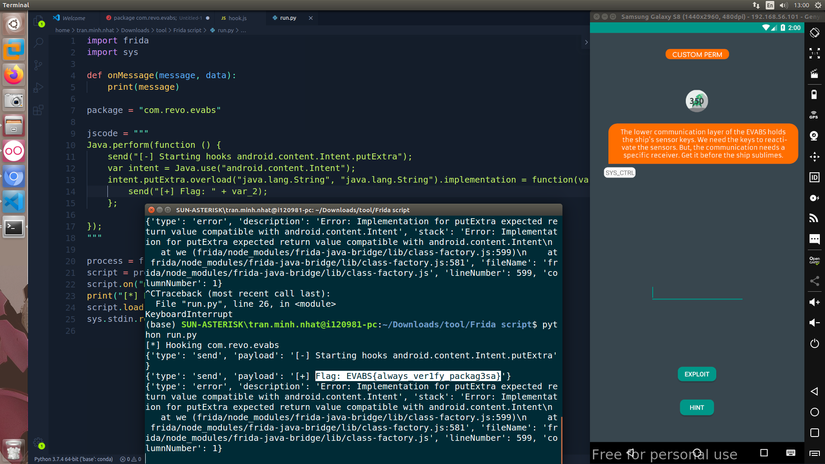
Here when I checked the flag, it reported a wrong flag, while I was quite sure that I was doing the right way. So I sent an email to ask the author of EVABS and received a reply that the way I did was correct. Because the random code has an error, the flag is wrong.
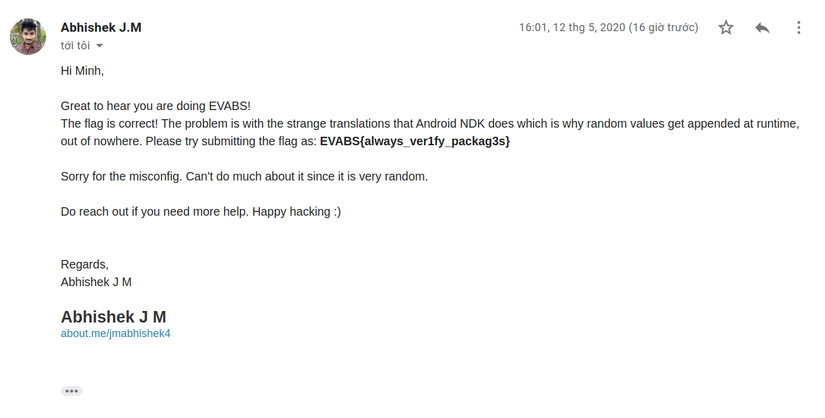
Thereby confirming that the Indian brothers are very enthusiastic
Level 12 – Instrument
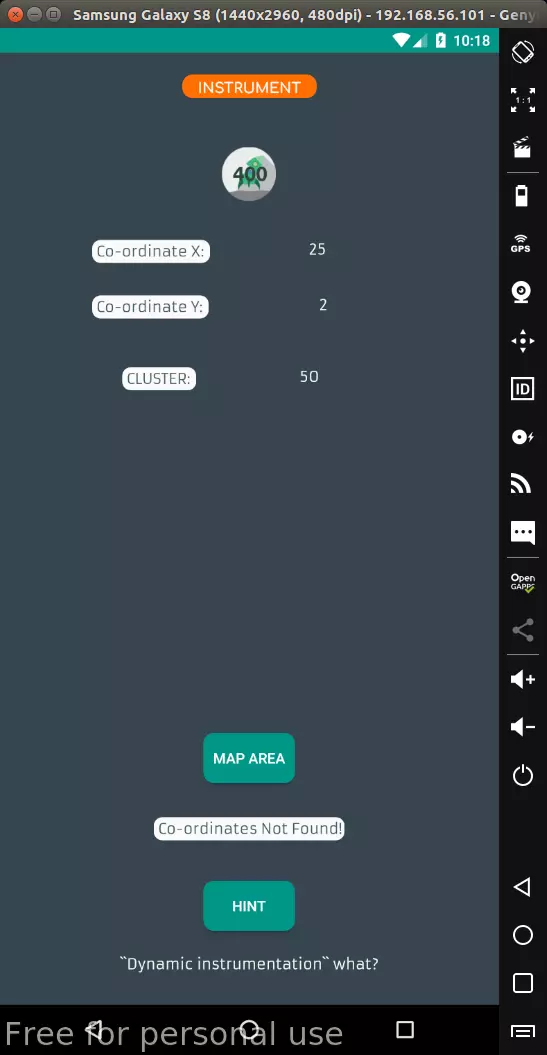
When “MAP AREA” is clicked, two x and y coordinates will appear with a value equal to x * y. This article also needs to use Frida to do, in my opinion, it is easier than level 11. Source code of level 12 in frida1.class file

The comparative logic of this article is very simple, the flag will be printed if (x = a * b)> var5 + 150 with var5 is an int random number in the range 0 -> 70. Because ab fixed makes x always 50 , so var5 random then whatever x is not satisfied. So, just hook and edit the nextInt (int) function for return -150, it’s fast without any thinking or calculation.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 | <span class="token keyword">import</span> frida <span class="token keyword">import</span> sys <span class="token keyword">def</span> <span class="token function">onMessage</span> <span class="token punctuation">(</span> message <span class="token punctuation">,</span> data <span class="token punctuation">)</span> <span class="token punctuation">:</span> <span class="token keyword">print</span> <span class="token punctuation">(</span> message <span class="token punctuation">)</span> package <span class="token operator">=</span> <span class="token string">"com.revo.evabs"</span> jscode <span class="token operator">=</span> <span class="token triple-quoted-string string">""" Java.perform(function () { send("[-] Starting hooks java.util.Random.nextInt"); var random = Java.use("java.util.Random"); random.nextInt.overload("int").implementation = function(var_1) { return -150; }; }); """</span> process <span class="token operator">=</span> frida <span class="token punctuation">.</span> get_usb_device <span class="token punctuation">(</span> <span class="token punctuation">)</span> <span class="token punctuation">.</span> attach <span class="token punctuation">(</span> package <span class="token punctuation">)</span> script <span class="token operator">=</span> process <span class="token punctuation">.</span> create_script <span class="token punctuation">(</span> jscode <span class="token punctuation">)</span> script <span class="token punctuation">.</span> on <span class="token punctuation">(</span> <span class="token string">"message"</span> <span class="token punctuation">,</span> onMessage <span class="token punctuation">)</span> <span class="token keyword">print</span> <span class="token punctuation">(</span> <span class="token string">"[*] Hooking"</span> <span class="token punctuation">,</span> package <span class="token punctuation">)</span> script <span class="token punctuation">.</span> load <span class="token punctuation">(</span> <span class="token punctuation">)</span> sys <span class="token punctuation">.</span> stdin <span class="token punctuation">.</span> read <span class="token punctuation">(</span> <span class="token punctuation">)</span> |
The flag will be printed as log:
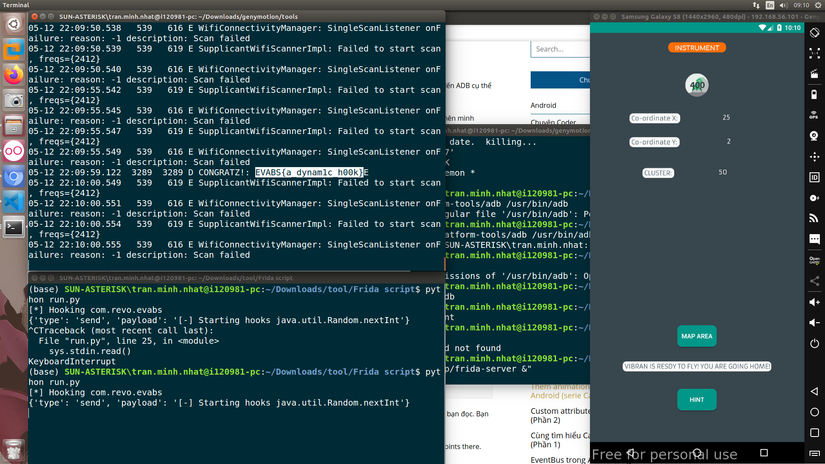
Check the flag is still wrong, probably still the same error as level 11: V